2. Controls Overview
Access Controls
Access controls are a core part of information security because they decide who can access organizational assets and what they are allowed to do. They do not only restrict access, but also allow the correct level of access to authorized users and processes while denying access to unauthorized ones.
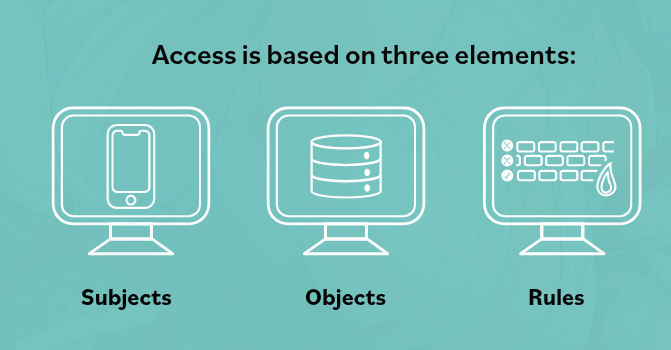
Subjects
A subject is any active entity that requests access to an asset. This can be a user, process, procedure, client, program, or device. A subject initiates the request for a service or resource and must have the proper permissions or clearance to gain access.
Objects
An object is anything a subject tries to access. It can be a file, database, computer, server, printer, communication resource, process, or similar resource. Unlike a subject, an object is passive. It responds to requests but does not initiate them.
Objects are usually protected by external access control mechanisms, and they may also have an owner who decides who can access them.
Rules
Rules are the instructions that determine whether a subject is allowed or denied access to an object. These rules compare the subject’s validated identity and attributes against an access control list or policy.
Rules can allow access, deny access, limit how much access is given, or apply conditions such as time-based access.
Simple Meaning
Access control works by using rules to decide whether a subject can access an object, ensuring only authorized access to resources.