40. Defense in Depth
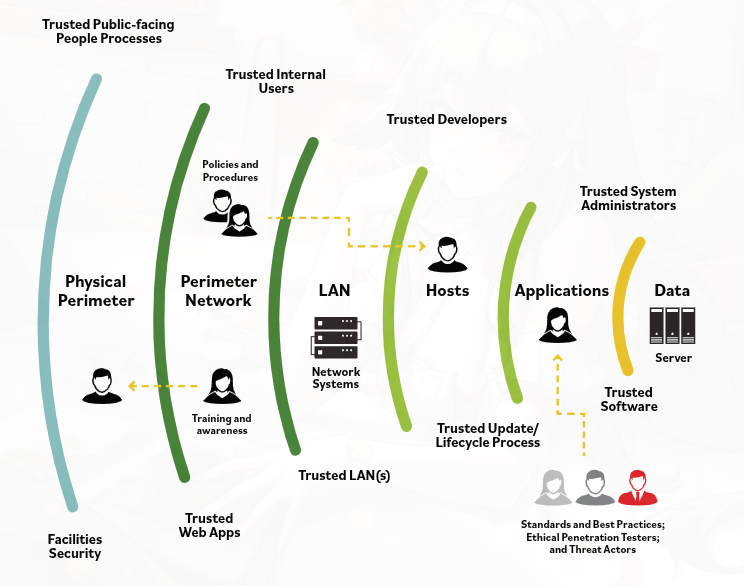
Defense in depth is a layered security approach. Instead of relying on one control, it uses multiple types of controls to protect the organization.
The idea is that if one layer fails, other layers still provide protection. This makes attacks harder and reduces the chance that one weakness will expose everything.
Defense in depth includes different control areas:
- Data – protects the actual data using controls like encryption, data leak prevention, identity and access management, and data security controls
- Application – protects applications using controls such as application firewalls, database monitoring, and data protection measures
- Host – protects endpoints using antivirus, endpoint firewalls, secure configuration, and patch management.
- Internal network – protects traffic inside the organization using IDS, IPS, internal firewalls, and NAC
- Perimeter – protects against outside access using gateway firewalls, DMZs, honeypots, and malware analysis
- Physical – protects facilities and hardware using locks, walls, and access control
- Policies, procedures, and awareness – administrative controls that reduce risk, support proper behavior, and help identify threats early
Main Idea
Defense in depth protects systems through multiple layers of administrative, technical, and physical controls.