38. Zero Trust
Zero trust is a security model that assumes no user, device, or system should be trusted automatically, even if it is already inside the network.
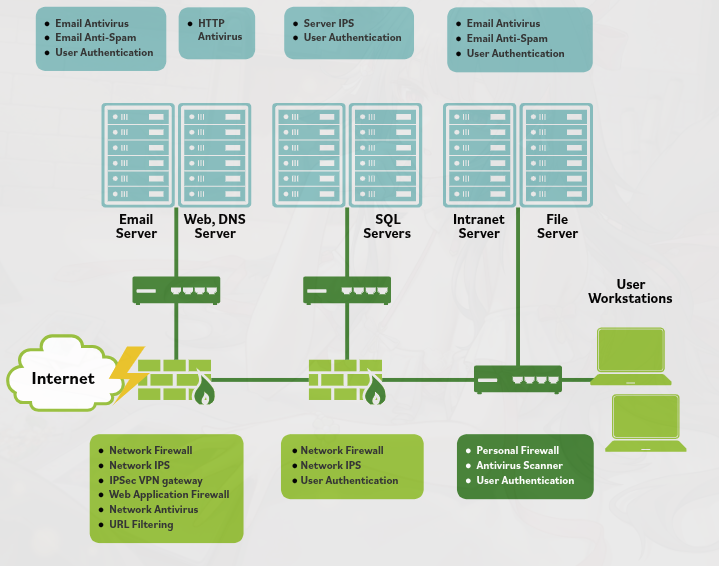
In traditional networks, once a user passes the perimeter security controls (like a firewall), they may have broad access across the network. Zero trust changes this approach by requiring verification at multiple points throughout the network.
Zero trust networks are usually microsegmented, meaning the network is divided into many smaller segments. Security controls such as firewalls, authentication systems, and monitoring tools are placed between these segments.
This design increases the chances of detecting suspicious activity early before it can spread across the network.
Zero trust focuses on protecting assets, services, and data directly, rather than relying mainly on the network perimeter.
Key characteristics of zero trust include:
- Continuous authentication and authorization
- Verification of users and devices before granting access
- Limited access based on least privilege
- Multiple security checkpoints throughout the network
Because access must be verified repeatedly, the window of trust is very small, reducing the ability of attackers to move freely within the network.
Main Idea
Zero trust security assumes no inherent trust and requires continuous verification to access network resources, protecting systems through microsegmentation and strict access control.