22. Asymmetric Encryption
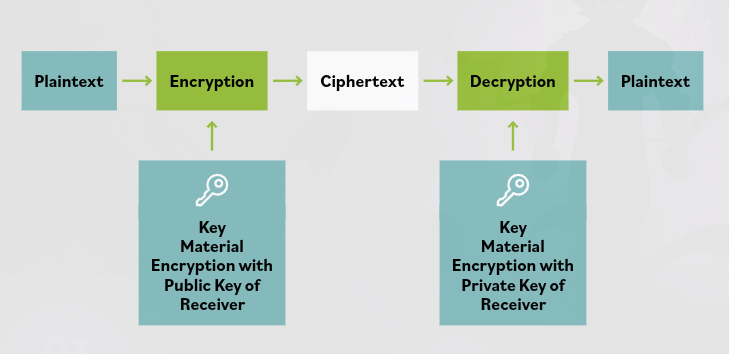
Asymmetric encryption uses one key to encrypt and a different key to decrypt the plaintext.
This is different from symmetric encryption, which uses the same key for both encryption and decryption.
Key Pair
To communicate using an asymmetric algorithm, a user first generates a key pair.
- One key is kept secret and is called the private key.
- The other key can be shared and is called the public key.
- Anyone can encrypt data using the recipient’s public key, but only the recipient can decrypt it using their private key.
Benefits
Asymmetric key cryptography solves the key distribution problem by allowing messages to be sent securely across an untrusted medium without exchanging keys beforehand.
It also supports features such as:
- Non-repudiation (a sender cannot deny sending the message)
- Access control
- Data integrity (ensuring data is not altered)
It also improves scalability, since each party only needs a key pair (one public and one private key).
Limitation
Asymmetric cryptography is much slower than symmetric cryptography. This is because it uses larger keys and requires more complex mathematical operations, which significantly reduces speed.
Example Use
The public key and private key must be used together as a key pair.
- A message encrypted with a public key can only be decrypted with the corresponding private key.
Similarly, a message signed with the sender’s private key can be verified using the sender’s public key.
To send a confidential message:
- The sender encrypts the message using the receiver’s public key.
- Only the receiver, with the private key, can decrypt and read the message.
This allows a confidential message to be sent across an untrusted channel.