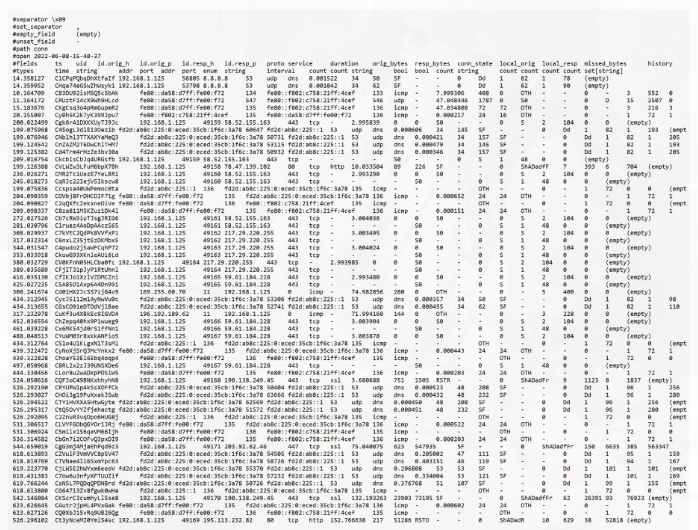
6. Data Security Event Example
A raw log (detailed system record of network or security activity) can show whether someone tried to access a secure file, scan ports, or attack a server.
Security engineers read these logs to identify things like:
- source (where the traffic came from)
- destination (where the traffic was going)
- port (which service or entry point was being used)
- protocol (communication method such as TCP or UDP)
- action/result (whether the traffic was allowed, blocked, or suspicious)
By analyzing this data, they can tell whether someone was using a normal secure port or a suspicious port to try to get into the system.
The main point is that security must be planned from the start. Logs help detect attacks, but they are only one part of security. A secure system must already be designed with protection in place before data enters the network.
Main Idea
Raw logs help detect suspicious activity and possible break-in attempts, but real security starts with proper planning and protection from the beginning.